The Russian “Hacking Scandal” Explained in Twelve Tweets
[guest post by JVW]
I thought this might be a good companion piece to Dana’s post from earlier today regarding the Obama Administration’s retaliation for alleged Russian hacking.
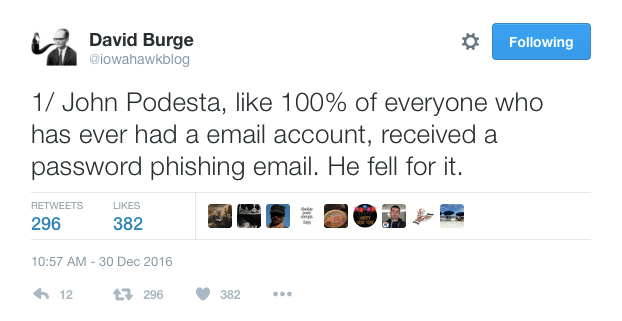
The estimable David Burge, who blogs (though, sadly, no longer) and tweets as Iowahawk, and who deserves the designation Public Intellectual far more than, say, Paul Krugman or Ta-Nehisi Coates do, sent out a series of twelve tweets earlier today which nicely explain why all of this kvetching over the supposed Russian interference in our recent election is way overblown. That is to say, in fewer than 1680 characters Iowahawk has provided way more clarity than the most ponderous think pieces at The Atlantic or Vox (though I’m admittedly setting the bar pretty low there). Behold the patient logic and careful explication:
For a guy who watched his campaign workers and major donors all get behind an effort to oust Benjamin Netanyahu two short years ago to now whine about “meddling” in another nation’s election just because somebody in Russia who may or may not have been working on behalf of Vladimir Putin managed to execute a crude and simpleminded phishing scheme on the most technologically-savvy campaign of all time is so laughably stupid that it could only come from this President and this Administration.
– JVW

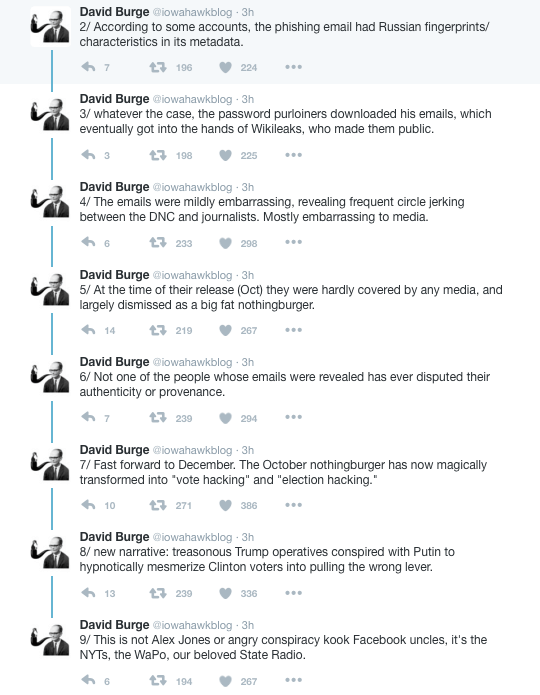
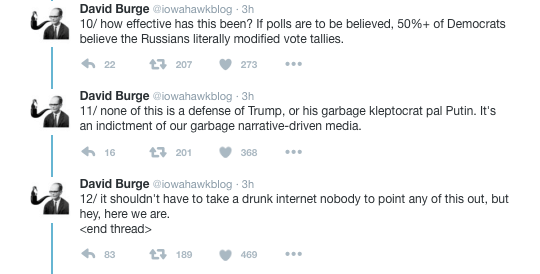


I think Iowahawk is right in that Democrats and their allies are now being led to believe that “Russian hacking” actually means manipulating vote counts in Pennsylvania, Wisconsin, Michigan, Ohio, and Florida, though there is zero evidence that this really happened.
JVW (6e49ce) — 12/30/2016 @ 3:08 pmHe has control of the mindstone?
narciso (d1f714) — 12/30/2016 @ 3:30 pmOh, come on. This election was rigged. Trump said it first, and then there were all the revelations about Russian (and who knows who else) subversion. There’s no way the 45th Presidency can be considered legitimate now.
The only way to fix it is for the states to hold an Article V convention and choose a new President and Vice-President untainted by foreign influences.
nk (dbc370) — 12/30/2016 @ 3:32 pmIowahawk is one of the very few people on earth who have my full support in using twitter. He is a master twitterer. He never embarrasses himself.
elissa (08e3c6) — 12/30/2016 @ 3:35 pmTroll level perseus, nk.
narciso (d1f714) — 12/30/2016 @ 3:36 pmReaders who don’t know that you like to jack people around for fun will be taking you seriously, nk. Take our current president’s advice and “cut it out”. I’m asking nicely. 🙂
elissa (08e3c6) — 12/30/2016 @ 3:39 pmHe’s very good iowahawk.
narciso (d1f714) — 12/30/2016 @ 3:41 pmsome of this *should* be a defense of Mr. Trump
who is what you get when you do for-reals democracy in your cowardly brokedick obama-raped slutstate
and i suggest you
lick
it
up
happyfeet (28a91b) — 12/30/2016 @ 3:44 pmJust a voice crying in the wilderness, that’s what I am. You guys would have called the police on Paul Revere for disturbing the peace.
nk (dbc370) — 12/30/2016 @ 3:44 pm“if i didn’t start painting, i would’ve raised chickens”
happyfeet (28a91b) — 12/30/2016 @ 3:48 pmmr john podesta just emailed me his american express card number along with the pin # and his mother’s maiden name
thank you mr podesta
Cruz Supporter (102c9a) — 12/30/2016 @ 3:58 pmi will enjoy my shopping spree at best buy
and my trip to tahiti
and a big donation to the hoover institution in your name of course
No way, let nk be nk!
Don’t change a thing, my man.
JVW (6e49ce) — 12/30/2016 @ 3:58 pmHE NEEDS TO STAY BE NK CAUSE OF A) THE VALUE OF CONSISTENCY PLUS ALSO B) THE CONTINUITY
happyfeet (28a91b) — 12/30/2016 @ 4:02 pmOnly someone as stupid as a ‘community organizer’ would fall for the fake news excuse for the Dems finally getting their long overdue and richly deserved comeuppance.
You just can’t fool enough of the people, enough of the time, to elect a crooked money grubbing blood-stained whore to the highest office in the land.
ropelight (78afaa) — 12/30/2016 @ 4:13 pmOh, make no mistake, I recognize Mr. nk has redeeming qualities. He has cleverly bought his gas, tobacco and booze products for less up in my (next door) county and therefore graciously drops his tax dollars for those items here. It is very much appreciated and shows excellent fiscal responsibility on his part.
elissa (08e3c6) — 12/30/2016 @ 4:16 pmGreetings:
I’ve pretty much always found the former Iowahawk (Iowa City ???) convincing but this time I still find myself unsure because Misses Clinton only got 92% of the vote in Washington D.C. and only 93% in Detroit.
11B40 (6abb5c) — 12/30/2016 @ 4:23 pmi need me some cheaper booze products dial a pikachu in why don’t you
happyfeet (28a91b) — 12/30/2016 @ 4:23 pmthe only hacking scandal is that barack and lurch have proven themselves to be a couple of hacks in the international arena this week
lurch is even married to a hack
when teresa was married to senator heinz, she was all republican and talkin’ the smack that teddy kennedy was a drunken lard-a*s
but then after senator heinz’ plane crashed and she soon married lurch, she turned into a democrat faster than the wonder twins could turn themselves into the form of an octopus on a motorbike
teresa reminds me of a portuguese water dog for some reason
Cruz Supporter (102c9a) — 12/30/2016 @ 4:34 pmWhich collar county, Elissa? I used to be a fiend for cheap gas and booze in Indiana under the skyway, but I grew tired of waiting on line behind the broke Horseshoe Casino types trying to scam the station attendants into getting free gas.
urbanleftbehind (847a06) — 12/30/2016 @ 4:35 pmCS, with regard to Lady Ketchup of Africa (remember that comment during the 2004 campaign) , I could see Melania getting a second run at Pennsylvania Ave. after Donny punches out.
urbanleftbehind (847a06) — 12/30/2016 @ 4:39 pmOt, awkward doings in Brazil.
Meanwhile in Paris, there is mischief afoot.
narciso (d1f714) — 12/30/2016 @ 4:42 pmTweet 5 from Хок из Айовы is wrong: the media gave that stuff plenty of attention.
And since it got people to focus on the negatives of Clinton and the DNC, and tamped down discussion of Trump’s negatives, that helped Trump.
But it was much of a nothingburger as Хок из Айовы suggests. As someone I know likes to say, if you don’t want to see how sausage is made, stay away from sausage factories.
Kishnevi (b4162e) — 12/30/2016 @ 4:45 pmI used to read iowahawk when he was a commenter at Little Green Footballs. How much the world has changed since then.
Gabriel Hanna (51348d) — 12/30/2016 @ 4:46 pmCarlos jhonson went to underverse and came back stranger.
narciso (d1f714) — 12/30/2016 @ 4:48 pmIn Paris there should always be mischief afoot.
Kishnevi (b4162e) — 12/30/2016 @ 4:51 pmBut what do you mean now? All I see is un freak-out over an an abandoned suitcase, and a seriously large number of four footed rats in the Marais.
They focused sporadically on the emails unlike with wilikileaks first iteration or Snowdon. The Panama papers hack was another unexploredbreach in the infosphere, which they wound down when it involved the wrong peoplr
narciso (d1f714) — 12/30/2016 @ 4:52 pmNk has been summoned way southward, though he could probably wait until March to go to Orlando for the Rebenga! moment.
urbanleftbehind (847a06) — 12/30/2016 @ 4:56 pmProspective mischief I should say, re a conference five days before the inaugural.
narciso (d1f714) — 12/30/2016 @ 4:56 pm4 years and 4 months too late, but AMBASSADOR LIVES MATTER!
urbanleftbehind (847a06) — 12/30/2016 @ 5:00 pmThat situation never happened at krone, there was a lively debate specially in the mid 70s, but that happened in the enclaves
narciso (d1f714) — 12/30/2016 @ 5:00 pmNot so much apparently, but the Olympics are over so need to hider the truth.
narciso (d1f714) — 12/30/2016 @ 5:03 pmThe wages of the Berlin attack – the Poles folding?
urbanleftbehind (847a06) — 12/30/2016 @ 5:07 pmhttp://mobile.reuters.com/article/idUSKBN14J1V9?il=0
#19 urbanleftbehind,
yes yes
once the mr donald’s time on this earth has expired
melania will be in demand
so will her inheritance
senator lindsey graham is single
she’ll have so much money that even mr barney frank will ask her out
Cruz Supporter (102c9a) — 12/30/2016 @ 5:38 pmbut i have a suspicion mr barney will take her to a chippendale’s revue on their first date
Now Sosa was based on a real character though.
narciso (d1f714) — 12/30/2016 @ 5:39 pmI would think it unlikely, she want born in this country, which was the implication.
narciso (d1f714) — 12/30/2016 @ 6:14 pmHF, thats too much pulchritude to waste on bearding…that type of job goes to swamp veterans like Ms. McConnell. Methinks a standard bearer of the white half of what replaces the D party has the best shot.
urbanleftbehind (847a06) — 12/30/2016 @ 6:33 pmOh, and the evidence that the Obama adminstration released regarding proving Russian involvement?
Its horse manure.
https://www.wordfence.com/blog/2016/12/russia-malware-ip-hack/
SPQR (a3a747) — 12/30/2016 @ 6:48 pmNow bezos is channeling ‘live free and die hard’, next week ultton’s
narciso (d1f714) — 12/30/2016 @ 6:49 pmBut they are continuing to push this Big Lie. Why? Is it so that they can pretend for 4 years that the election was “stolen” and that the people secretly yearn for the return of Sauron?
Or are they preparing for something more immediate, such as a nullification of the election, backed by all necessary force?
Kevin M (25bbee) — 12/30/2016 @ 7:04 pmShades of mccarry’s Shelley’s heart, although in that one the CIA successor agency actually hacked the voting systems, to keep the democrat in office.
narciso (d1f714) — 12/30/2016 @ 7:16 pmIf it wasn’t enough that Trump has been making himself look bigger with his growing list of quality administration appointees, now Obama has now embarked on making himself look as small as possible – he’s finally found something he’s good at.
Glory days.
ThOR (c9324e) — 12/30/2016 @ 7:20 pmThe Left always seeks to de-legitimize their opponent. That’s Alinsky Objective #1.
That’s why racism was blamed, then James Comey, then it was the voting machines, then Russian “hackers,” and then finally the Electoral College.
But it looks like Russian “hackers” is going to be their default position since it can’t be proven or disproven — thus the silly allegation will be able to continue to be buoyed by the MSM, tactical left wingers, and low information Americans who don’t know any better.
Ultimately, I guess Mitt Romney was correct about Russia, huh, Barack? (LOL)
Cruz Supporter (102c9a) — 12/30/2016 @ 7:25 pmSPQR–
Thank you for that. The WOrdPress security experts concluded:
1. DHS provided us with 876 IP addresses as part of the package of indicators of compromise. Lets look at where they are located. The chart below shows the distribution of IP addresses by country.
(Chart shows that well over 90% of the addresses originated in “Unknown”; “USA” or “Russia” in that order. About half were “unknown). Many TOR exit nodes were included.
2. The IP addresses that DHS provided may have been used for an attack by a state actor like Russia. But they don’t appear to provide any association with Russia. They are probably used by a wide range of other malicious actors, especially the 15% of IP addresses that are Tor exit nodes.
3. The malware sample is old, widely used and appears to be Ukrainian. It has no apparent relationship with Russian intelligence and it would be an indicator of compromise for any website.
Kevin M (25bbee) — 12/30/2016 @ 7:34 pmDave Barry’s end of year 2016 review is out in case you have not seen it.
http://www.miamiherald.com/living/liv-columns-blogs/dave-barry/article123321019.html
elissa (fb4013) — 12/30/2016 @ 7:36 pmThanks elissa, Dave Barry outdid himself, own he’ll need a chiropractor.
narciso (d1f714) — 12/30/2016 @ 7:49 pmAnd speaking of the Russians…..From the Star Tribune:
The utility involved was not named by the anonymous government sources.
Or, maybe it’s more akin to a bird dropping by somebody in government or media who wants to bolster a certain narrative, stat.
CNBC Update via tweet:
elissa (fb4013) — 12/30/2016 @ 8:06 pmGrizzly Steppe
I know they’re all lawyers and haven’t a clue about technology, but they are making this Romper Room attack look like something out of William Gibson when it is something most grammar school kids would laugh at.
WHY are they doing this? It’s beyond belief. It’s also beyond belief that the press is letting them get away with it. It’s pure BS, worse than the dread Cairo video.
Kevin M (25bbee) — 12/30/2016 @ 8:22 pmThat’s all they have in Their bag of tricks, kev, it dorsnr stand up to cursory examination.
narciso (d1f714) — 12/30/2016 @ 8:26 pmLetting them get away with it? The press is fully complicit. If you google grizzly steppe you will see the headlines and proliferation in various and increasing media outlets over the past 20 hours or so. It has all the earmarks of a planned and planted propaganda scheme such as was exposed in some of the DNC wikileaks pieces. I do not think it’s wise to dismiss or diminish the dangers of hacking and infiltration of systems by Russia or CIA or anybody. But this particular news nugget out of nowhere clearly has a purpose which has little to do with “protecting the grid”.
elissa (fb4013) — 12/30/2016 @ 8:41 pmwhen jihadists blow people up or shoot up gay nightclubs in florida, then barack & company say we never know what their motive was
Cruz Supporter (102c9a) — 12/30/2016 @ 8:48 pmbut when democrats lose an election, then all of a sudden they become a magic eight ball and intuit their motives without reservation
and without evidence
Looks like the prop or nit debacle, contract taibbi, the AMD claims wrrr more firmly established, they gave the name and description of the facilities, the Germans didn’t say how much of an asset cyrveball was, and the top CIA division people didn’t ask.
narciso (d1f714) — 12/30/2016 @ 8:53 pmOK narciso, you are going to have to translate that one!
elissa (fb4013) — 12/30/2016 @ 8:56 pmThere ate parallels with the missile gap, certain officials fed certain reporters like Stewart also this story, yet the u-2 surveillance proved otherwise
narciso (d1f714) — 12/30/2016 @ 8:56 pmTaibbi makes the point, trying to cover himself about curveball. But that want the whole story, they kept finding caches not huge stockpiles
narciso (d1f714) — 12/30/2016 @ 9:00 pmIs that any clearer, people I know who are in the business, say these crumbs are very dubious.
narciso (d1f714) — 12/30/2016 @ 9:05 pmThis reminds me very much of when Ben Rhodes, one of President Obama’s top national security advisers promoted a made up narrative and led gullible journalists to believe a misleading timeline of U.S. negotiations with Iran over a nuclear agreement. Rhodes relied on clueless and inexperienced reporters to create a reverberating “echo chamber” that helped sway public opinion to seal the Iran deal.
https://www.washingtonpost.com/lifestyle/style/obama-official-says-he-pushed-a-narrative-to-media-to-sell-the-iran-nuclear-deal/2016/05/06/5b90d984-13a1-11e6-8967-7ac733c56f12_story.html
elissa (fb4013) — 12/30/2016 @ 9:09 pmBay Area air resources board try to blame Chevron.
Chevron says it wasn’t them. The problem is San Francisco stinks. It really really stinks.
Why does San Francisco smell?
So blind people can hate them too.
I’m not getting over that headline anytime soon.
papertiger (c8116c) — 12/30/2016 @ 9:13 pmYes the rhodes road show rides again. He’s the one that told the mail among other that putin had to know.
narciso (d1f714) — 12/30/2016 @ 9:14 pmActually the oxidation of dimethyl sulfide (DMO) causes the distinct used diaper smell of San Fran.
https://wattsupwiththat.com/2016/11/04/friday-funny-impact-of-sea-smell-overestimated-by-present-climate-models/
The fact that the air resource board is addressing this thing by accusation toward industry shows they’re useless as an accordion at a duck hunt.
papertiger (c8116c) — 12/30/2016 @ 9:24 pmWell, there’s a lot of smelly San Francisco poop, too.
http://www.dailywire.com/news/12001/san-francisco-requires-poop-maps-help-pedestrians-hank-berrien
elissa (fb4013) — 12/30/2016 @ 9:29 pmKevin @46, if you’re a Democrat, you want to believe all this stuff, and so it is in the DNC’s interest to keep their dwindling base “happy”. This fiction is now being embellished despite its obvious shortcomings. It is yet another example of “Fake News”. In fact, I suspect the current uproar over “Fake News” is another thrust by the same people. They hope that their feigned outrage over FN will inoculate them from being suspected of perpetrating yet another FN campaign. And if you are a member of the Democrat base, the ploy will work, yet again.
The WordFence/WordPress link provided by SQPR at #36 is excellent. WordPress captured and dissected the malware that the administration is so concerned about. It is used by hackers around the world, and the authors ask for a donation. The authors appear to be from the Ukraine. It is ubiquitous. And anyone who uses the internet knows that danger lurks in every email encouraging you to use the enclosed link to access your account. Children have grown up with this knowledge for two decades. That is why Hillary! should be considered a very reckless and irresponsible person, deserving of felony charges and a trial by her peers.
My wife gave me an excellent book on the subject of computers, spying, and the internet. It is Cyber Spies by Gordon Corera. I’m about half way through, and it brings back many memories from the 70s and 80s. As an outsider looking in, you kind of understood what was happening, but the details and personalities are fascinating.
If you run into some lefties over the New Years weekend, don’t be surprised if they lecture you on both the election that the Russians gave to Trump, and the issue of Fake News. Both, of course, pointing to the the need for adult supervision of the internet by good people like themselves. They might even believe that the Russians controlled the electronic voting machines that a British company, owned by Soros, has been providing to Democratic-controlled jurisdictions. Be kind to them. They need to believe these fictions, just as Communist Party members had to embrace the latest Party line in the Soviet Union. It’s for their mental “health”.
BobStewartatHome (c24491) — 12/30/2016 @ 10:15 pmnarciso, it occurs to me that the NSA will have a heck of time using word search techniques to pull your essays out from the clutter for a “proper examination”. They’ll have to rewrite an awful lot of software, and they’ll need the next generation of super computers to link the various topics and personalities into what often appears to be a coherent thought.
I am beginning to suspect that you are harboring antisocial thoughts. Shall I notify the Committee, Comrade?
BobStewartatHome (c24491) — 12/30/2016 @ 10:25 pmWords I want to hear Trump say to the DC press corps:
“You people are worse than Goebbels!”
Kevin M (25bbee) — 12/31/2016 @ 12:40 amThey need to believe these fictions, just as Communist Party members had to embrace the latest Party line in the Soviet Union.
Coincidentally, I’ve been binge-watching “The Americans.” The spies are constantly trying to get info on new US technology (stealth, ARPAnet, etc), never once asking why the US creates all this new stuff and why their continent-spanning empire is so bad at it.
Kevin M (25bbee) — 12/31/2016 @ 12:44 amOn Jan 21st, Congress ought to haul the NSA’s CTO up before a committee and ask him “How did this hack happen on your watch?” Hopefully, he’ll respond “Because we can’t prevent stupid people from doing stupid things. Most children know better than to click on an email link asking for their password.”
Kevin M (25bbee) — 12/31/2016 @ 12:47 amThe bigger issue is the willful ignorance of most of the American electorate. If the folks were not this weak of mind and so willing to simply demonize opposition, the media would have failed long ago.
It’s all a giant deflection (Look! Squirrel!) which takes up the space and energy an otherwise serious media would dig into BHO’s treachery to Israel, and his unprecedented rule-making as his term ends.
Ed from SFV (3400a5) — 12/31/2016 @ 12:57 amIt is helpful to the busy purveyors of the Grizzly Steppe narrative that Vermont is the scene of the alleged grid attack (that by careful reading one can gather they admit did not actually reach or even come close to the grid).
Friday night, Vermont Gov. Peter Shumlin (D) kept it going by calling on federal officials “to conduct a full and complete investigation of this incident and undertake remedies to ensure that this never happens again.”
The Obama administration’s late inning UN Israel treachery did not go over well and has gotten way more push back (both in the media and from the general public including within their own party) than they expected. So they realized they needed a very big and immediate “Look! squirrel!!”. The Russian hacking risk publicity is an obvious deflection as others have already pointed out. Plus the Dems are also looking ahead to the Tillerson confirmation battle in which Russia will be a large part of their playbook in that fight.
I have been concerned about potential threats to both the electric grid and to the water supply for a long time. That concern continues unabated. But a genuine or imminent security threat to the grid (or to the actual presidential election) would not be being prosecuted in the press and blogs through anonymous “government officials” leaking to friendly journalists. We are living in a very interesting but also a very treacherous and unstable situation right now. The president-elect and Priebus need to be very careful not to be goaded into saying or doing anything foolish for the next 20 days especially with respect to Russia and Putin.
elissa (42bfd8) — 12/31/2016 @ 4:39 amhttp://www.sfgate.com/bayarea/article/Human-waste-shuts-down-BART-escalators-3735981.php
steveg (5508fb) — 12/31/2016 @ 5:41 amYes, corera’s a very good guide, in lieu of an onion router, I’m as samizdat as possible.
narciso (d1f714) — 12/31/2016 @ 6:55 amelissa, I’ll bet that some hacker, call him the NSA, already has copies of the email instructing Shumlin to make this announcement. And if we learn about the coordination of this campaign via some “leak”, then the story will not be about the “squirrel!” conspiracy, but rather the ungentlemanly behavior of the leaker.
It is a tradition of what used to be the American media that we can assume a politician lies most of the time. But even with this forewarning, the best of them leave us wondering if this time they are telling the truth, even when they utter the most fantastic tale. Is it through subliminal cues that they somehow get us to suspend disbelief? Given their known proficiency, it is useful to remember that when one of these creatures utters the words “… that [what ever] never happens again!”, never is an awfully long time.
BobStewartatHome (c24491) — 12/31/2016 @ 7:19 amSamizdat may have worked against the Stasi’s hundred kilometers of files prior to the collapse of the iron curtain, but extra precautions are warranted today.
BobStewartatHome (c24491) — 12/31/2016 @ 7:37 amSpeaking of onion routers, Amazon has a special today. Coincidence??
BobStewartatHome (c24491) — 12/31/2016 @ 7:41 amIntersting, the firm film to consider this was alden Robinson’s sneaker, there was sort of a mad tech genius played by Ben kingsley, but he was just the Mcguffin, it was the last days if bush, so it was the nsa that was the villain, the net posited a similar scenario.
narciso (d1f714) — 12/31/2016 @ 7:54 amI am no expert, but as an attentive padawan here and in other places I ask some basic questions.
narciso (d1f714) — 12/31/2016 @ 7:57 amso they assumed in the crowdstrike report, certain fixed elements, the Russian characters, the targets, and the time of coding, but those are not immutable,
https://www.wordfence.com/blog/2016/12/russia-malware-ip-hack/
narciso (d1f714) — 12/31/2016 @ 8:06 amthey also examine the hacked utility, but start with the basics
http://www.robertmlee.org/critiques-of-the-dhsfbis-grizzly-steppe-report/
now taibbi by contrast, treats all weakly sourced reports as the same,
narciso (d1f714) — 12/31/2016 @ 8:08 amgrizzly stupid
happyfeet (28a91b) — 12/31/2016 @ 8:16 amyour favorite squeeze toy, snowden likely did much more damage Pikachu,
narciso (d1f714) — 12/31/2016 @ 8:20 amhe’s such a scamp
happyfeet (28a91b) — 12/31/2016 @ 8:23 amat the time of the chapman ring, that in part targeted nsa, the mole who ran them, suggested there were more,
http://libertyunyielding.com/2016/12/31/rudy-giuliani-obamas-intel-russia-incompetent-politicized/
narciso (d1f714) — 12/31/2016 @ 8:32 amTo coin a term, Trump is being “Katrinaed.”
Kevin M (25bbee) — 12/31/2016 @ 9:20 amAlso coining the past tense form of verbs ending in “A”
Kevin M (25bbee) — 12/31/2016 @ 9:21 amOr past participle, anyway.
Kevin M (25bbee) — 12/31/2016 @ 9:22 amThe sasquach hunters found a torn up beaver dam on a swampy corner of “John Podesta’s” estate. Hold Bigfoot responsible.
Read all about it in the next issue of UFOlogy magazine.
papertiger (c8116c) — 12/31/2016 @ 9:55 amYou all might like to believe in Bigfoot, but me, I think it was an inside job.
Podesta’s pond was declared a protected bird sanctuary by the EPA last year.
papertiger (c8116c) — 12/31/2016 @ 9:59 amIt’ll be better when President Trump is in charge.
So so much better.
Just hang in there you guys.
happyfeet (28a91b) — 12/31/2016 @ 10:38 amthe follow up piece,
http://www.robertmlee.org/analytical-leaps-and-wild-speculation-in-recent-reports-of-industrial-cyber-attacks/
narciso (d1f714) — 12/31/2016 @ 10:56 amIf I were John Podesta I am pretty sure that after all the wikileaks disclosures I would be too embarrassed and too ashamed of myself to be seen in public or to speak on any issue of actual importance. I guess we’re all wired differently, though, huh?
elissa (c57762) — 12/31/2016 @ 11:00 amthat would require shame, and not having the 65 rizzotto tray carriers behind you, like a conga line,
narciso (d1f714) — 12/31/2016 @ 11:13 amIf I were John Podesta I am pretty sure that after all the wikileaks disclosures I would be too embarrassed and too ashamed of myself to be seen in public or to speak on any issue of actual importance. I guess we’re all wired differently, though, huh?
One of my favorite things about this story is that it involves John Podesta. I only wish that James Carville and George Stephanopoulos had also effed-up somehow too.
JVW (6e49ce) — 12/31/2016 @ 11:13 amHow do we know it wasn’t Nigeria? Technology is fungible, highly mobile, and Nigerians are the world’s preeminent phishers.
n.n (b35206) — 12/31/2016 @ 1:07 pmIt’ll be better when President Obama isn’t in charge.
FIFY.
Kevin M (25bbee) — 12/31/2016 @ 1:31 pmHow do we know it wasn’t Nigeria?
It could have been Mexico!
Build that wall!
Kevin M (25bbee) — 12/31/2016 @ 1:32 pmI only wish that James Carville and George Stephanopoulos had also effed-up somehow too.
I wish Soros had lost all his money to the Nigerian prince.
Kevin M (25bbee) — 12/31/2016 @ 1:33 pmThe stink in San Francisco has been pinned down. Started last Wednesday.
Turns out it was just Nancy Pelosi home for the holidays.
http://www.msn.com/en-us/news/us/something-smells-funky-in-san-francisco/ar-BBxJ7YX?fb_comment_id=1210676489019217_1210712385682294#f2bbb7fe7643a88
papertiger (c8116c) — 12/31/2016 @ 1:57 pmExcellent post.
One other thing (hinted at in the post). Everything about the hacking relates to revelation of true emails about the DNC. In other words, more true information to the voters. There is ZERO evidence that vote counts were tampered with. So at the end of the day, the worst you can say is that the voters were given more information about the DNC than they would have been given otherwise. Isn’t transparency a good thing?
Bored Lawyer (541e02) — 12/31/2016 @ 4:47 pmBut now Trump is tired of others being in the limelight and announces he has sekret info that he will only reveal after a few days of intense media speculation.
Kevin M (25bbee) — 1/1/2017 @ 9:26 amThere are some problems with what Iowahawk tweeted.
1. John Podeasta did not “fall” for it.
As revealed in a Wikileaks dump…
(https://wikileaks.org/podesta-emails/emailid/34899)
John Podeata, or his assistants, who may also have had access to his Gmail account, contacted the IT experts at hillaryclinton.com for advice, because this phshing email looked more real to him tahn others he had previously received, being as it reported a failed attempt to log on to his account in Ukraine – without explaining why it was denied, and that kind of implied someone has his password but they log on was unsuccessful because Google had an algorithm that said fraud. Credit card sometimes reject trasactions that are perfectly legitimate on a technical level, and GMail has a superb spam filter, so it was plausible that this cold be legirimate.
And they were told by IT expert Charles Delavan that the e-mail was genuine, and he should change his password as soon as possible, and also, not quite as urgently, to turn on two-factor authentication.
Delavan gave him a Google link to do both (but did not insist on it)
Because they were not ready to turn on two-factor authentication right away (or maybe ever) and because it sounded like you’d have to do both if you used the link Delavan gave, and because of the possibility of locking him out of his account if they did both, and because it was still urgent to change his password, and because his assistants did not have his phone, they chose to merely change his password and for that used the bit.ly link provided in the “legitimate” email instead. That link did not require you to set up two-factor authentication but would let you just change the password alone.
Delavan at first was reported by the New York Times that he meant to say it was an illegimate e-mail, but later told Slate that his mistake was leaving out the word “NOT.”
2. The John Podesta hack is not the only one linked to Russia, just merely perhaps the most obviously tied to Russia. It wasn’t the first hack, and it wasn’t the first released.
3. The Podesta email was covered by the media.
http://www.nytimes.com/2016/10/30/us/politics/neera-tanden-wikileaks.html <blockquote version of this article appears in print on October 30, 2016, on Page A20 of the New York edition with the headline: Leaks Lay Bare a Longtime Clinton Adviser’s Unflinching Straight Talk The main thing it revealed was that John Podeata was not a true insider.
Sammy Finkelman (d41c9f) — 1/1/2017 @ 10:32 am1. JVW (6e49ce) — 12/30/2016 @ 3:08 pm
That poll may be kind of misleading. Offering something as a choice causes people to think the pollsters know something they don’t.
The real confusion is over what Barack Obama told Vladimir Putin to cut out. People like to say he ddin’t cut it out.
It wasn’t spying that Obama told Putin to cut out – it was any attempt (which probably wasn’t happening, because it’s impossible) to manipulate the vote count.
By which they meant to include even the unofficial vote count, by which they did think was possible, even if all they could do was take down web sites.
They also wanted him to stop leaking, which may have happened, or come close to happening, except maybe for the fake story about the pizza place in Washington D.C. that supposedly was holding childrn prisoner for purposes of pedophilia with the bosses of the operation being Hillary Clinton and John Podesta.
I don’t know if they have linked that story to Russia. Maybe it has been linked:
http://www.japantimes.co.jp/news/2016/12/22/world/politics-diplomacy-world/russias-disinformation-campaign-caught-u-s-off-guard/
Sammy Finkelman (d41c9f) — 1/1/2017 @ 10:44 amCruz Supporter (102c9a) — 12/30/2016 @ 4:34 pm
She didn’t become aDemocrat until 2003 when John Kerry was gearing up to run for president. John Heinz died in 1991, they began dating in 1993 and married in 1995.
https://en.wikipedia.org/wiki/Teresa_Heinz
Sammy Finkelman (d41c9f) — 1/1/2017 @ 10:48 amon an *ice* motorbike
happyfeet (28a91b) — 1/1/2017 @ 11:02 amlet’s keep it real
happyfeet (28a91b) — 1/1/2017 @ 11:02 am#100 Sammy,
Come on, she may not have officially changed her voting registration to “Democrat” until 2003, but she flipped a switch as soon as she began dating Democrat John F. Kerry.
Cruz Supporter (102c9a) — 1/1/2017 @ 11:12 amMaybe pointing out of the sanctioned outfits is a cyber security firm.
narciso (d1f714) — 1/1/2017 @ 11:19 amSammy,
Podesta sent if off to his IT guy, who told him to change his password. The IT guy provided a bona fide link to Google. Podesta clicked the phishing link in the original email instead.
So, it is truthful to say that he “fell for it” especially in a 140-character tweet (doubly so as the tweet was in response to someone else’s claim that tweets were too short to explain the details).
His IT guy was wrong not to call it completely bogus and to be ignored, but Podesta is the one who clicked the bit.ly link.
Kevin M (25bbee) — 1/1/2017 @ 12:23 pmAlso, sending someone a “log in here so I can steal your password” email is not a “hack” any more than “3 card monte” is “theft.” The “attack” has been around since AT LEAST 1970, when I first ran across it as a timeshare login shell. Anyone with the wit to avoid losing at tic-tac-toe should be able to navigate this dire hazard.
Kevin M (25bbee) — 1/1/2017 @ 12:28 pmBTW, yesterday it was all the news about this “hacking” but now you can’t see anything about it. The WaPo story about the utility hack disappeared right after the “corrected” the first 5 paragraphs out of existence.
Kevin M (25bbee) — 1/1/2017 @ 12:32 pmamazon turdlord jeffy bezos sucks at making fake news even more than he sucks at making music apps
happyfeet (28a91b) — 1/1/2017 @ 1:07 pmKevin, it takes a lot of players to keep Fake News afloat. Lately, the enthusiasm seems to be deserting the collaborators, and for the first time in my memory, their sorry little fantasies have been sinking beneath the waves within days of their launch. Even Schumer has seen the futility of the recent efforts. The only media-certified gravitas-endowed Senators willing to participate are the senile wing of the GOPe, McCain and such like.
They’ll have to restart the whole mechanism from scratch right after the inauguration. Homeless guys living on the street within sight of the White House, 40 million Americans without medical care, seniors withering on the vine, its all in their old play books. And they can even spice it up with real news, like part timers at the local coffee shop being dragged before Federal magistrates to compel payment of their student loans. Or disabled veterans having their reenlistment bonuses clawed back because their injuries make it impossible for them to fulfill the terms of their enlistment. Of course, these will not be linked to the Obama administration which is doing those things right now. Oh the anguish, the gnashing of teeth, the pulling of hair … it will be like old times. But this time around, the weaponized bureaucracy will be also be able to help pull the wagon. The CIA can revel deep state secrets implicating any number of foreign powers in a conspiracy to read our emails on the internet. My gosh, can you imagine that? What scoundrels! Their agents even watch our cable television and drive around taking pictures of our facilities.
The political class and their hand maidens in the media are nothing if not persistent.
BobStewartatHome (c24491) — 1/1/2017 @ 1:36 pmBy the way, it occurs to me that one important difference between a conservative and a libertarian is that the latter must be shocked by the possibility that foreign powers might engage in reading our mail. Shocked! How can the world work if we don’t all play fair?
BobStewartatHome (c24491) — 1/1/2017 @ 1:43 pmZor security is run by a white hat hacker, they do protective strategies not offense.
narciso (d1f714) — 1/1/2017 @ 1:53 pmDelingpole has some helpful suggestions.
narciso (d1f714) — 1/1/2017 @ 1:55 pmShocked! How can the world work if we don’t all play fair?
“Gentlemen do not read each other’s mail.”
Kevin M (25bbee) — 1/1/2017 @ 4:20 pm— Secretary of State Henry L Stimson.
Bob, I hope to see things lamenting the plight of former government employees now standing in line for the benefits they once handed out. With any luck they’ll be complaining about the service.
Kevin M (25bbee) — 1/1/2017 @ 4:22 pmA lot of those “benefits” come with conditions that impoverish the recipient, and guarantee future poverty. Yes, it would be nice seeing some of Obama’s minions consigned to the mercies of our welfare state.
BobStewartatHome (c24491) — 1/1/2017 @ 4:26 pmSo there wAS even less to this story, than I suspected, the software is Ukrainian, there is no appreciable tie to the gru
narciso (d1f714) — 1/1/2017 @ 4:55 pm@narcisco:the software is Ukrainian, there is no appreciable tie to the gru
Wouldn’t have mattered if it HAD been Russian. If the lead pipe that killed Colonel Mustard in the library says “made in China” on it, is that evidence Xi Jinping was involved?
I have it on good authority that many components of John Podesta’s laptop were made in China. Maybe Xi Jingping WAS involved.
Gabriel Hanna (51348d) — 1/1/2017 @ 5:04 pmBow the dhs says there wee no maple state hacking.
narciso (d1f714) — 1/1/2017 @ 5:06 pmNot quite.
The libertarian view is that whatever foreign governments do, does not legitimize the US government spying on its own citizens.
Kishnevi (871225) — 1/1/2017 @ 5:07 pmChildren can and do carry out phishing attacks. Had a college roommate whose Gmail password got phished by a 14 year old.
20-year-old David Kernell “hacked” Sarah Palin’s Yahoo account by using the password recovery feature and typing in what high school she went to and her birth date.
I am astounded by how low an IQ the median journalist and pundit must have, and how ignorant of basic computer technology. Even more astounded when commenters I’m familiar with swallow it hook, line, and sinker.
Gabriel Hanna (51348d) — 1/1/2017 @ 5:09 pmRemember they ran that narrative, before the election, in esquire i think, or Ga its hard to tell the metrosexual publications apart, the other was about fox as a sex cult.
narciso (d1f714) — 1/1/2017 @ 5:21 pmKishnevi, and how do libertarians plan to deal with the reality that many who claim to be citizens are not? Even those who are citizens have proven themselves capable, since the dawn of written history, of selling their services to foreign interests, especially homicidal hordes besieging a city. And you may have noted that the Europeans are attributing their bad behavior in the 20th Century (Britain excluded) to excessive nationalism, which is basically having pride in citizenship. So libertarians are the root of all evil?
BobStewartatHome (c24491) — 1/1/2017 @ 5:25 pmThe evidence was weak on that score as well, but enough for the Murdoch’s to use it as a lever against ailes
narciso (d1f714) — 1/1/2017 @ 5:27 pmTake David from, bezis lead tech reporter is an refugee from city paper. Debonis
narciso (d1f714) — 1/1/2017 @ 5:54 pm105. Kevin M (25bbee) — 1/1/2017 @ 12:23 pm
What the IT guy told him to do was to change his password “immediately” and also to ensure that ensure that two-factor authentication was turned on his account.
And he said to do both he should use the link he supplied.
But his people were not ready to turn on two-factor authentication (for reasons that aren’t clear, but it might be because his Gmail account was accessed from many devices, and it would be quite a chore, or maybe they might lock him out of his account, certainly if they did it too quickly)
They didn’t want to do BOTH. They only wanted to do ONE.
Remember, both the IT guy and psuedo-Gmail said changing the password should be done immediately. The IT person had said it was absolutely imperative that this is done ASAP.
The IT guy had also said that “This is a legitimate email” which would mean that that link was legitimate as well. And since they only wanted to change the password they used the other link, the one that would only change the password…
The advantage over the one the IT person supplied was that you could change the password without also having to set up 2-step verification. The way Charles Delevan wrote what he wrote it sounded like maybe you couldn’t do that with his link.
Sammy Finkelman (022db5) — 1/1/2017 @ 5:58 pmNo, it was the IT guy who fell for it!
And what he told him was that it was a legitimate e-mail, which meant that it would be perfectly safe to click on link contained in that e-mail. Not ideal, because he’d only change his password that way, but safe, and after all, according to that e-mail, Google didn’t seem to think it necessary for him to set up 2-factor authentication, but only to change his password.
The IT guy claims he left out the word not and he should have typed: This is NOT a legitimate email.
But if so, the rest of the message would not be the same, because he woudn’t tell him to change his password immediately because of the risk he would use the link. And it would NOT be imperative to change his password as soon as possible, because nobody had it! Instead somebody was trying to get it!
Sammy Finkelman (022db5) — 1/1/2017 @ 6:05 pmSammy, what Kevin said is all we need to know. What’s your point? That Podesta needs a nurse maid. If so, say so.
This is like Leviticus claiming that minorities have a beef over their treatment since the 1970s. Life is a challenge. And we all face different challenges. Podesta stumbled over a rather mundane issue, but stumble he did. And I rather doubt Putin was anxiously awaiting his fail. I still admire Teddy Roosevelt for his determination to rise to the occasion, despite his childlike political philosophy. He had a point, and it still applies. All this concern over how tough it is to get along in today’s world is a terrible thing to pass on to our children. Just do it.
BobStewartatHome (c24491) — 1/1/2017 @ 6:08 pmJohn Podesta did have some questions about the phishing e-mail, and so he asked the IT person at hillaryclinton.com if it was genuine, and he got an answer that it was. Of course he would rather have contacted Google, but the e-mail came from no-reply@accounts.googlemail.com. You know these big Internet companies like Amazon and eBay have customer service where it’s very hard to get in contact with a person. So instead he contacted IT support at hillaryclinton.com, even though actually he was not using a hillaryclinton.com address.
The fake email could sound somewhat plausible to John Podesta because credit card companies sometimes reject trasactions that are perfectly legitimate on a technical level, solely because of an algorithm, and GMail has a superb spam filter. John Podesta could therefore think that maybe the message was true and someone had his password, but that, like the phishing e-mail said, similar to the way a credit card company might decline a transaction that was made in Europe, Google had anyway stopped the fraud from logging in because the log-in was attempted from Ukraine.
GMail, in fact, occasionally sends people genuine messages about log-ins done from other devices, so GMail does look like it’s on top of things.
Of course Google doesn’t STOP the log-in in case it comes from a suspicious location, if 2-step verification isn’t in place, and it doesn’t send a notification of a possily suspicious log-in to the same e-mail address that somebody tried to log into. It sends a notice of a successful log-in it to an alternate e-mail address.
Sammy Finkelman (022db5) — 1/1/2017 @ 6:19 pm127. BobStewartatHome (c24491) — 1/1/2017 @ 6:08 pm
What Iowahawk and Kevin said about Podesta falling for the phishing e-mail is wrong. It was Charles Delavan, the IT guy, who fell for it (despite his denials)
Lots of people need a nursemaid when it comes to computers. It was the nursemaid who failed. It was perfectly logical for Podesta to click on that bit.ly link once he was told the e-mail was genuine.
The Hillary Clinton people themselves used a bit.ly link.
His e-mail message ends:
Sammy Finkelman (022db5) — 1/1/2017 @ 6:29 pmThe previous regetence to frum, comes from a five the nation piece, that althouse excepted.
narciso (d1f714) — 1/1/2017 @ 6:36 pmSurprise Surprise Surprise.
The Washington Post has retracted its story about Russian hackers penetrating the nation’s electricity grid with a virus found in a Burlington, Vt., electric company laptop.
“Authorities say there is no indication that Russians had penetrated the US electric grid,” according to an editor’s note attached to a corrected version of the story on the paper’s Web site.
elissa (2e76f6) — 1/1/2017 @ 6:38 pmKevin M:
If you understand things right, even when you’re very brief, you’ll find other words.
The password purloiners by the way, didn’t just download his e-mail once – in March – they kept reading it all the way through till around the end of August, at which point apparently they lost access. It was made public starting in early October.
The biggest revelation from the Podesta e-mails was the text, or some of the text and some full speeches, of Hillary Clinton’s secret speeches, and even the Q & A as well as someone’s analysis of what could be problematical there.
And even an e-mail from one speechwriter explaining how he put something in one speech so it could be used as a defense.
Here’s the New York Times writing about it;
http://www.nytimes.com/2016/10/16/us/politics/wikileaks-hack-hillary-clinton-emails.html
The New York Times found the following humorous:
Also:
None of this mattered very much.
Sammy Finkelman (022db5) — 1/1/2017 @ 6:45 pmI sincerely hope the WaPo retraction is a result of a lawsuit from officials at Vermont’s Burlington Electric Co. and that they will be duly compensated from Mr. Bezos’ wallet.
elissa (2e76f6) — 1/1/2017 @ 6:50 pm131. Here we have, again, some part of the intelligence community wanting to show dangers that are actually implausible.
Tyhe Russians did actually get into the electricity of Ukraine.
http://www.cbsnews.com/news/russian-hacks-into-ukraine-power-grids-may-be-a-sign-of-things-to-come/
Sammy Finkelman (022db5) — 1/1/2017 @ 6:50 pm(December 21, 2016, 7:27 PM)
Well if they were using Ukrainian software. But there were more holes in this narrative than a bloc of jarlsberg.
narciso (d1f714) — 1/1/2017 @ 6:56 pmWell, we have idiot Trump saying that no computer can be made safe.
Mr. Trump, for less than $2,000,00, I had my office computer assembled by the computer people next door. It had no modem. The only public thing it was plugged into was the electrical outlet. The scanner and the printer were on cables. If “hackers” wanted my clients’ files, they’d have to break into my office.
nk (dbc370) — 1/1/2017 @ 6:58 pm@nk:If “hackers” wanted my clients’ files, they’d have to break into my office.
Well, Tail-gunner, can they break in, or talk their way in? If they can, then your computer has not been made safe. There is no system that can defend against physical presence very long.
Gabriel Hanna (51348d) — 1/1/2017 @ 7:01 pmJuliet Eilperin and Adam Entous were the byline reporters of the original WaPo grid story. Will they pay any price at all for taking the anonymous “government official’s” propaganda at face value and slinging it far and wide out to the public? Will all the other papers, websites and blogs which copied it or referenced their exclusive as the source also retract the “story” as the fake news that so many of us had pegged it for from the get go?
Yeah, silly question.
elissa (2e76f6) — 1/1/2017 @ 7:02 pmnarciso @130. Face the Nation piece that Althouse excerpted.
This is the Althouse blog post that quotes David Frum.
http://althouse.blogspot.com/2017/01/on-face-nation-today-panelists-seemed.html
I heard that, too.
I found more interesting this, which Jeffrey Goldberg didn’t take in taht quite-specific-to-Donald-Trump-alone way.
http://www.cbsnews.com/news/face-the-nation-transcript-january-1-2017-book-panel-political-panel/
DAVID FRUM: Let me give you an example of something we should all be very frightened of. And this may be the single most dangerous thing for world peace that happens. It’s very bad when a president, as Barack Obama did, draws a red line and the red line isn’t actually there. That’s humiliating. That leads people to misunderstand. What is much more dangerous is if the president says the red line isn’t there and it really is. Trump is everyday signaling– signaling that red lines aren’t there, that NATO doesn’t matter.
A bit later:
JEFFREY GOLDBERG: Look, Saddam had this in Kuwait. Saddam felt that the U.S. was signaling that it would have been okay to invade Kuwait, take it as your own. There were mistaken signals sent. Saddam went, and then there was a reaction. And we all know what the reaction was. So this is– there is precedent in the presidency for this to– to happen.
You could also mention, of course Dean Acheson and South Korea in 1949 or 1950 wheneer it was.
Althouse also did a post on Meet the Press:
http://althouse.blogspot.com/2017/01/chuck-todds-emotional-journalism.html
Sammy Finkelman (96f386) — 1/1/2017 @ 7:07 pm138. elissa (2e76f6) — 1/1/2017 @ 7:02 pm
The story never made any sense to me. I listened carefully. How was he grid going to be affected? what exactly was infected? I was waiting for some detail that explained why this was a danger and it never came. It just didn’t seem to add up. They were talking about it like it was maybe the Stuxnet virus.
Sammy Finkelman (96f386) — 1/1/2017 @ 7:11 pmIf you understand things right, even when you’re very brief, you’ll find other words.
Sammy, how would you know?
Kevin M (25bbee) — 1/1/2017 @ 7:11 pmGabriel Hanna (51348d) — 1/1/2017 @ 7:01 pm
Here again, Hillary’s Clinton server was an exception, because it was gurded by the Secret Service.
Her e-mail account was probably the most secure e-mail account in the history of e-mail.
On her end, she carefully guarded her Blackberry, and sometimes even Huma Abedin couldn’t gain access to it, which she needed to use her own clintonwmail.com account.
Of course, all the government experts are saying it was not secure, it must have been hacked etc.
Sammy Finkelman (96f386) — 1/1/2017 @ 7:16 pmChris cooper who did a much better Hansen than rob Lowe, explained to his FBI ptotege in breach, with certain irony. The shortfalls in FBI handling classified materials.
narciso (d1f714) — 1/1/2017 @ 7:26 pmI see that your disingenuousness is at full throttle across all the threads tonight, Gabriel.
nk (dbc370) — 1/1/2017 @ 7:37 pmThe journal still has the old story up, with a sorry about that explanation buried in the piece.
narciso (d1f714) — 1/1/2017 @ 8:25 pmThe Washington Post should just claim that the Russians hacked The Washington Post and published this fake news story about the grid in Vermont in order to make The Washington Post look bad. (LOL)
Cruz Supporter (102c9a) — 1/1/2017 @ 8:32 pmHe gets like that sometimes. Best thing to do is ignore him for at least 24 hours. That’s what I do.
Patterico (4fc3f4) — 1/1/2017 @ 8:56 pmEilperin is askydragin acolyte, extreme environmentalist, entous had not hereto fore displayed such hack behavior, but it all depends on your sources.
narciso (d1f714) — 1/1/2017 @ 9:06 pmForbes also takes up the debunk, now imagine if another event happens and there is a series of misunderstandings like with able archer.
narciso (d1f714) — 1/1/2017 @ 9:16 pmI will, Patterico.
Happy New Year!
nk (dbc370) — 1/1/2017 @ 9:21 pmThat last was when the soviet’s misinterpreted Reagan’s posture on nuclear weapons deployment and use.
narciso (d1f714) — 1/1/2017 @ 9:39 pmJuliet Eilperin gives it another go!
https://www.washingtonpost.com/world/national-security/russian-government-hackers-do-not-appear-to-have-targeted-vermont-utility-say-people-close-to-investigation/2017/01/02/70c25956-d12c-11e6-945a-76f69a399dd5_story.html
elissa (a33edd) — 1/2/2017 @ 9:05 pm